Silent Phone
Secure team communications. Enterprise-ready. No new hardware needed.
Your team's discussions are your business only. Silent Phone lets your team communicate remotely with complete security while being easy to deploy and use.
Silent Phone makes sure your conversations are 100% private and that you're connected only to your intended party. All encryption is done on device. No one can listen in.
Make secure calls with your existing iOS and Android devices. There are no special headsets or SIM cards. You don't need a single-purpose phone. With Silent Phone, no new hardware is required.
Silent Phone is easy to deploy and manage in an enterprise environment. It requires no end-user training. It supports SSO, SIEM systems, and can be deployed via MDM. You and your team will have a dedicated client liaison and direct access to our highly trained technical support staff.

We protect brand name enterprises, international NGOs, government agencies, and firms in such industries as defense, energy, and law. With Silent Phone, you're getting a premium product with top-notch security.

Keep the conversation going from anywhere in the world. Silent Phone delivers unlimited worldwide calling and messaging between your users with no hidden or additional fees from us.
Stored data is a security risk. Many providers keep as much data as possible "just in case." We keep as little data as possible. We don't track IP addresses or keep logs of calls and messages between users.
Most good things in the world start with a private conversation. Silent Phone lets your team talk securely across oceans and time zones.
We host a global network of servers to make sure that your calls connect wherever you are.
Silent Phone's powerful Security Words let you verify your own security.
Handle multiple calls at once with ease. Silent Phone shows you all your calls in one place. Pull calls into a conference, or let the other members speak for a moment while you pull someone aside privately.
Hear and be heard clearly with Silent Phone's HD quality voice and video. Our technology ensures that privacy does not come at the cost of call quality.

We think text should be as secure and as ephemeral as a call. With Silent Phone's Silent Text messaging, you can securely send messages, voice memos, documents, videos, images, and other files.
Messages you send are automatically deleted on all devices after the burn timer has expired. You can adjust the burn time between one minute and 90 days.
You can select a message for immediate destruction at any time. Burning the message causes it to be deleted from all devices of all parties in the conversation.
Silent Phone makes it quick and easy to record and send a voice memo. These are great for sending quick thoughts when you're out and about. Voice memos provide a secure alternative to voicemail.
Situational awareness helps your team move faster. Silent Phone lets you know when your messages have been delivered and when they have been read.
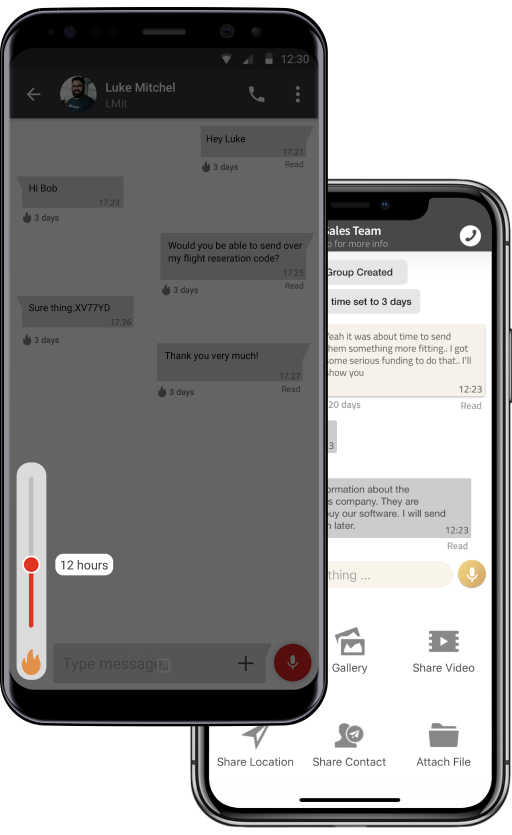
Silent Phone enables secure team collaboration with secure conference calling and secure group messaging. As you would expect from Silent Circle, your team's communications are encrypted end-to-end.
Most conference calling products mix the conference audio in the cloud, risking your secrets. Silent Phone mixes the conference on device. This enables Silent Phone to provide the same high level of end-to-end security to conference calls as it does for one-to-one calls.
Keep everyone in the loop by creating a secure text channel with your entire team. Unlike other products that store your group's messages in the cloud, Silent Phone keeps all of your content on device, keeping your team and its secrets safe.
Simply search by name or by email to contact your team members. Silent Phone makes sure your team members can find each other easily.
Call or message your team members directly from the contacts app on your phone. Silent Phone makes this easy, and also allows storing your Silent Phone contacts to your contact book.

Silent Manager helps you manage your team's users, groups, plans, and devices via the web. Add users with "zero-touch" deployment. Disable and delete users. Change a user's plan. Remotely wipe data from a device. Create groups and assign managers with scoped authority. Control your enterprise-wide settings. Integrate with other identity providers. It's all there.
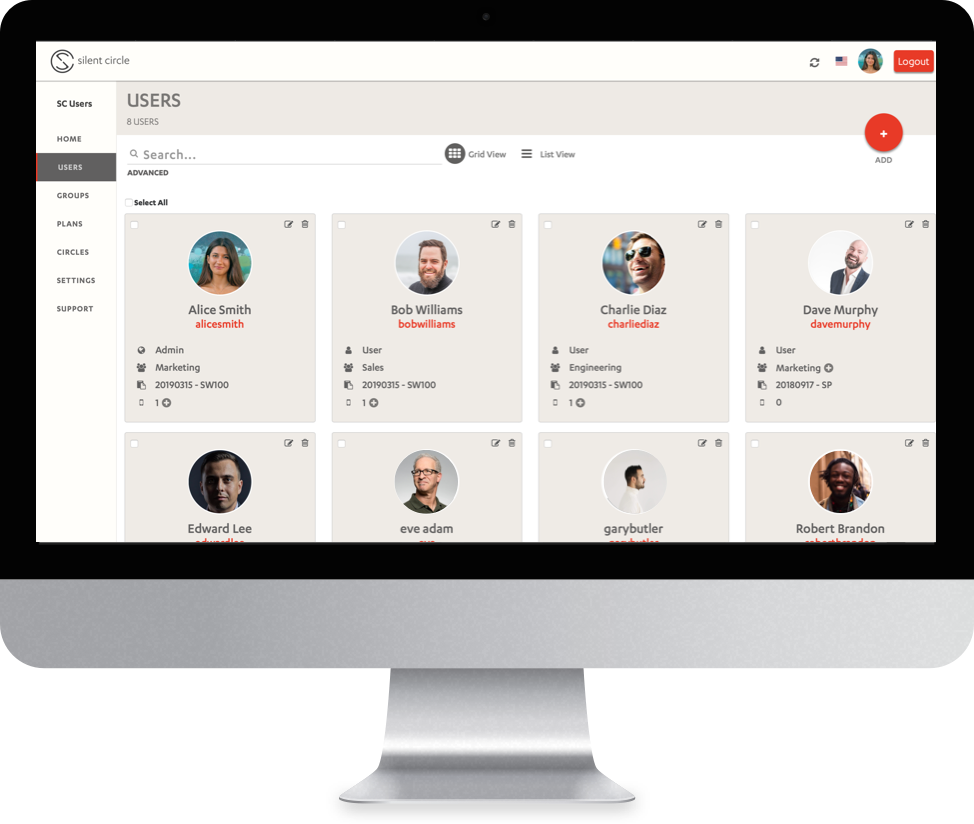
Deploy secure communication across your organization with no hardware, maintenance, or training required. Manage from the web, active directory, supported identity providers, or an existing MDM.
Learn moreSilent Phone supports Single Sign-On using OpenID Connect (OIDC) and Active Directory Federation Services (ADFS).
Contact salesSilent Phone offers unlimited user to user secure calling and messaging. With Circle-in-Circle, you can securely connect outside partners and vendors with your team.
Contact salesSilent Phone's Security Words put you in control of your own security. This unique system forms a "last line of defense" to keep man-in-the-middle attackers out of your communications. It's just one way that we go the extra mile to protect our customers. Here are the three steps to make your calls extra secure.
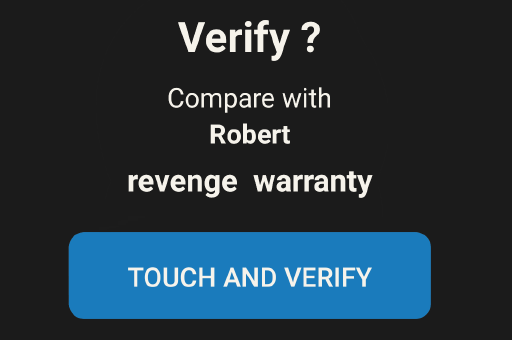
On a call, you'll be prompted with two Security Words.
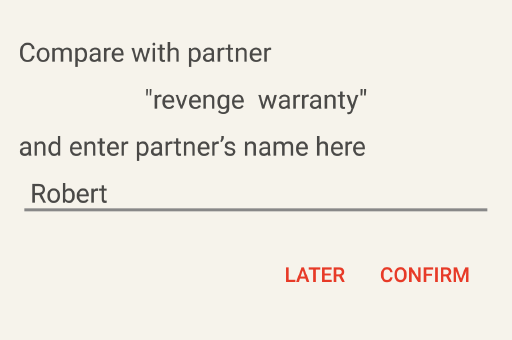
Both you and your partner should read both words to each other. Be sure that you both see the same words on the screen.
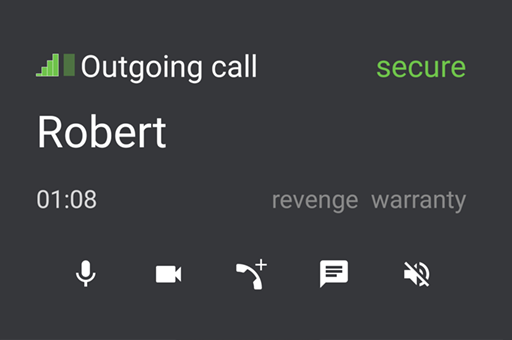
Tell Silent Phone that you have compared the words and that they match. Silent Phone will show that the call is "Green Secure" and will remember this for the next call. You only have to do this verification once per pair of devices.
Your team's communications aren't safe unless you're using a high quality end-to-end encryption product. We engineer Silent Phone to keep businesses like yours safe. Silent Phone uses ZRTP, the most secure telephony standard ever developed.
Learn more