Enterprise solutions for secure mobile communications
We deliver industry-leading end-to-end secure communications for teams. Silent Phone is easy to deploy and manage in an enterprise.
Contact sales
Communicate securely wherever you are in the world. Silent Phone delivers secure voice and video calling, messaging, file transfer, and more. End-to-end encryption makes sure no one can listen in.

Silent Phone is easy to deploy and manage in your enterprise and requires no end-user training.
Silent Phone users enjoy unlimited user-to-user calling and messaging from anywhere in the world.
Make secure calls with your existing Android and iOS devices without any custom hardware.

Work securely with your team from anywhere with Silent World, our premium package for the traveling C-suite.

Make the world your office with Circle-in-Circle, which provides all the benefits of an on-prem solution with worldwide availability, and without the hassle, maintenance burden, and lead time.
Our API-driven security information tools integrate with your in-house systems, giving your team real-time situational awareness about the security posture of all your team's members, wherever they are in the world.
Protect your team from increasingly sophisticated SS7 attacks which can reveal your location.
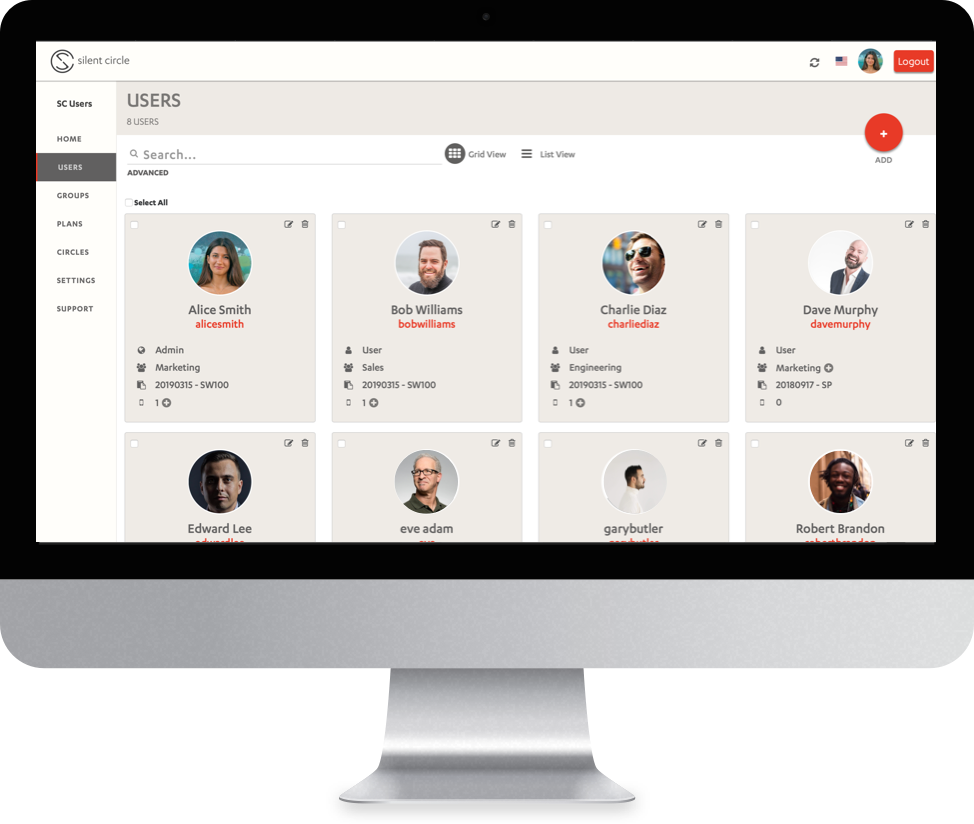
Silent Manager lets you create and manage users and groups, delegate administration, implement and enforce policies, assign licenses, remotely wipe data, and handle other administrative tasks for your organization.
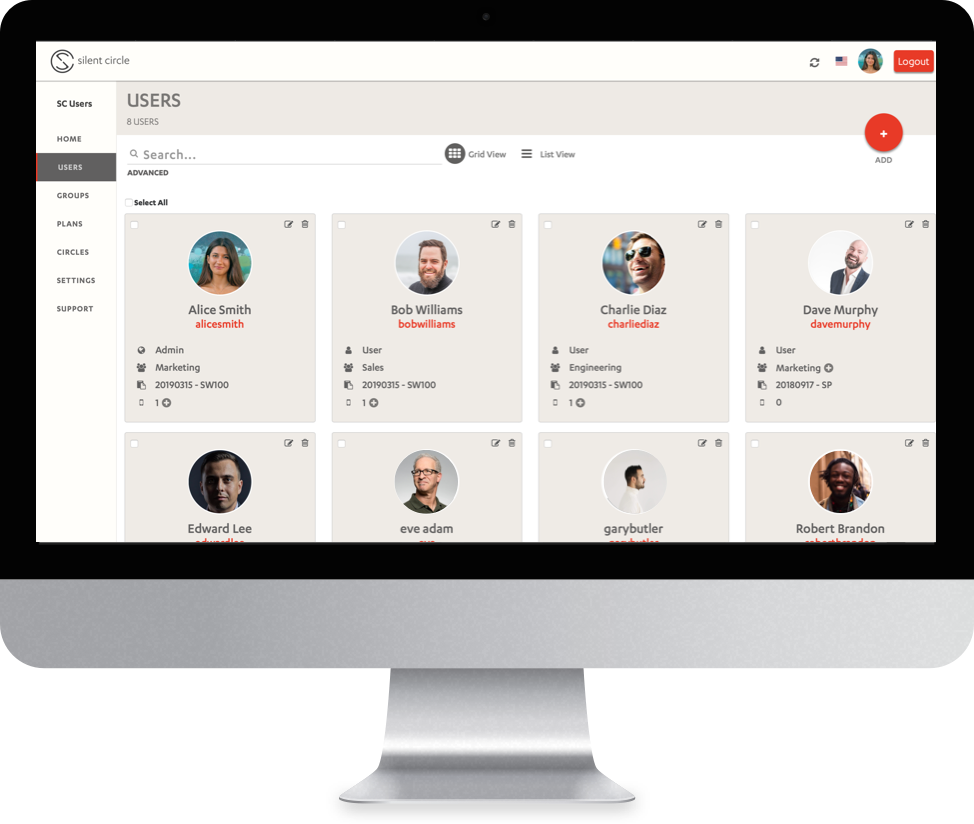
Use Silent Manager to deploy Silent Phone to your organization. Create users in bulk, one at a time, or via automatic provisioning with Single Sign-On.
When a device is lost or compromised, you want its sensitive data destroyed immediately. Silent Manager lets you remotely wipe all Silent Phone data from any device in your organization.
Get all the benefits of an on-premises installation without the expense and hassle of building and maintaining your own infrastructure.